So I started testing out some ideas last night.
I had heard mentioned that some people are using the Brownie Ethereum testing package to interact with DeFi, which I thought was fascinating, so I’d been meaning to take a look. I’ve got a bit of experience working with Hardhat, but I’ve been working with Python and was looking forward to doing more work with it. One of the fascinating things I read was that you can specify an external contract address and it will download the verified source code from Etherscan for it.
I’ve been spending a fair amount of time watching the Uniswap factory to catch new LPs going up. I caught a lot of scam tokens going up and blew through half an Eth chasing after new projects. There’s a lot of bot activity, and I really need to figure out how to make my own. Asynchronous programming is something that’s been giving me trouble, and I need to figure it out.
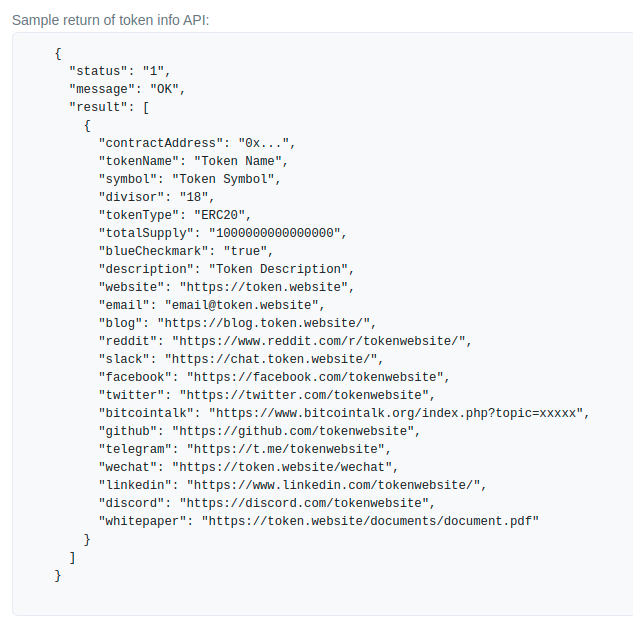
My plan is to build a bot that can watch the blockchain (and mempool) for these new Uniswap pool creation events. The events return the component pair addresses, so these tokens must be looked up as well to get the data. My vetting process while watching Merv.Tech’s new Uni page has been to lookup the token address on Etherscan to get the token symbol, then use their token lookup page for the same symbol to see if the token is legit. There are a lot of scams out there. By this point I can usually tell whether a project is legit or not. The trick is automating this as much as possible.
I had about a 50% hit rate after randomly throwing money at new pools. There were a lot that were straight fakes and rugs, and I may have stumbled across one or two that weren’t proper ERC20s and had some kind of mechanism to prevent selling. For a short-term sniping opportunity, the key is getting in as soon as the pool is launched, so actually watching the mempool for these type of transactions is going to give a bit of an edge.
I was able to put together short script that can call the Alchemy API and get the on-chain event logs. Now I have to figure out how to turn it into a websocket that can watch it in real time. That will be something that I’ve never done before. An async function watching a websocket. If I can get that to just log the events, then the next step will be doing the token lookups. I’m not sure if Alchemy is the best place to do that, as Etherscan has a API that can make sure we’re looking at a legit token.
Coingecko might be a good place to check as well.
One user story that we could build out would be to dump the token description and website details into our Discord server, just so we could keep an eye on it. Of course eventually we would want it to execute trades on it’s own. Even further, if I could find a way to scope new token creations from blockchain directly or from Etherscan, Coingecko or Dextools, we might be able to find and vet targets more easily.
Exciting times.